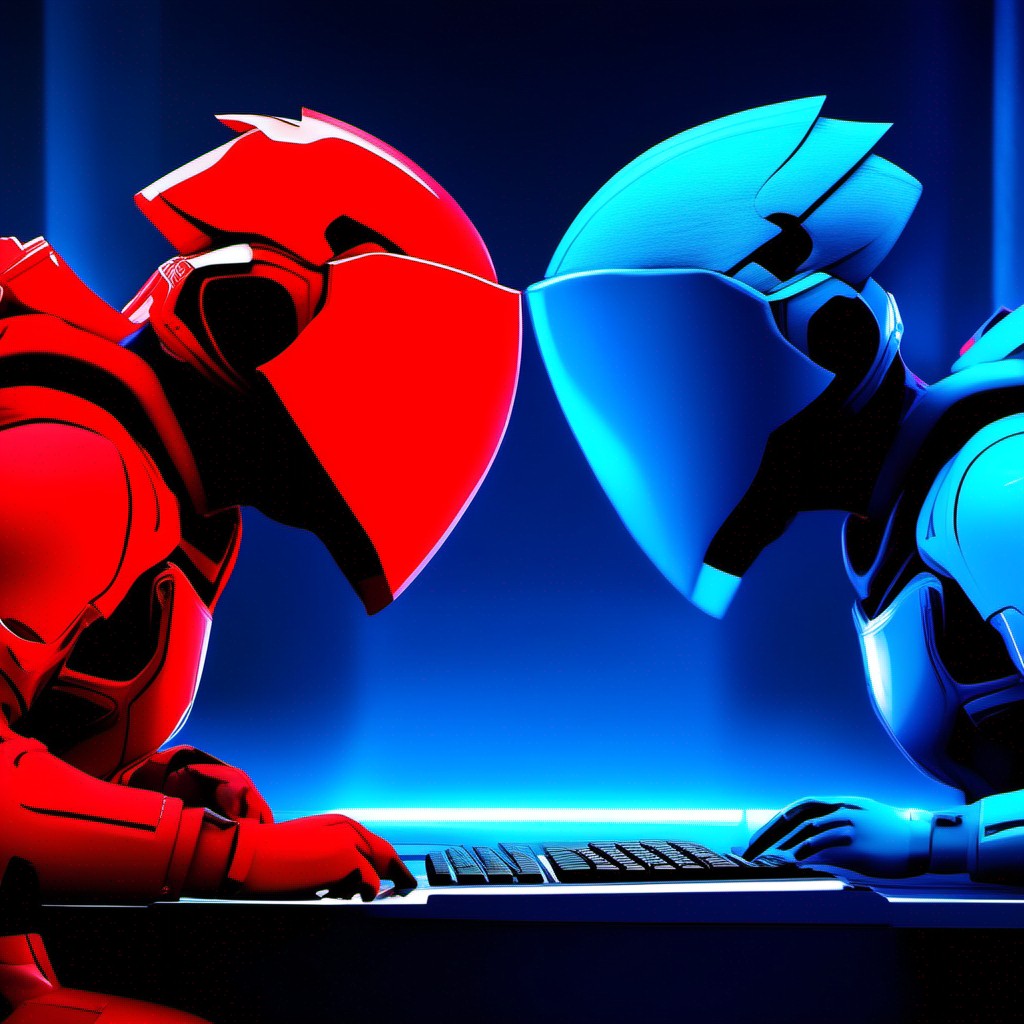
Penetration testing, a cornerstone of modern cybersecurity practices, empowers organizations to proactively identify and address vulnerabilities. Join us as we delve into the key phases of penetration testing and discover...
As businesses navigate the complexities of a digital era, ensuring a robust and resilient security system is paramount. At SafeNet, we understand the critical importance of continuous testing in fortifying...
As cyber threats evolve, so too must the tools and methodologies designed to defend against them. One such indispensable practice in the realm of cybersecurity is penetration testing, and at...
Two key practices that play a crucial role in this quest are vulnerability scanning and penetration testing. At SafeNet, we understand the distinctions between these approaches and their unique contributions...
Penetration testing, or pentesting, emerges as a proactive strategy to identify and address vulnerabilities within digital systems. At SafeNet, we understand the importance of a comprehensive approach to penetration testing....
At SafeNet, we recognize the importance of certified penetration testing experts in fortifying digital defenses. In this blog post, we’ll guide you through the journey of becoming certified for penetration...
Establishing a Security Operations Center (SOC) is a pivotal step in fortifying your organization against cyber threats. However, the journey doesn’t end with its establishment. Operating and maintaining a SOC...
At SafeNet, we understand the importance of building a Security Operations Center that serves as the nerve center of your cybersecurity strategy. In this blog post, we’ll guide you through...
Web app testing emerges as a crucial practice to fortify your digital assets against ever-evolving cyber threats. At SafeNet, we recognize the imperative need for comprehensive web app testing, and...
At SafeNet, we understand the critical role that web app testing plays in fortifying your digital infrastructure. In this blog post, we’ll delve into the world of web app testing,...